SQL Injection: Engineering for Vibe Coders
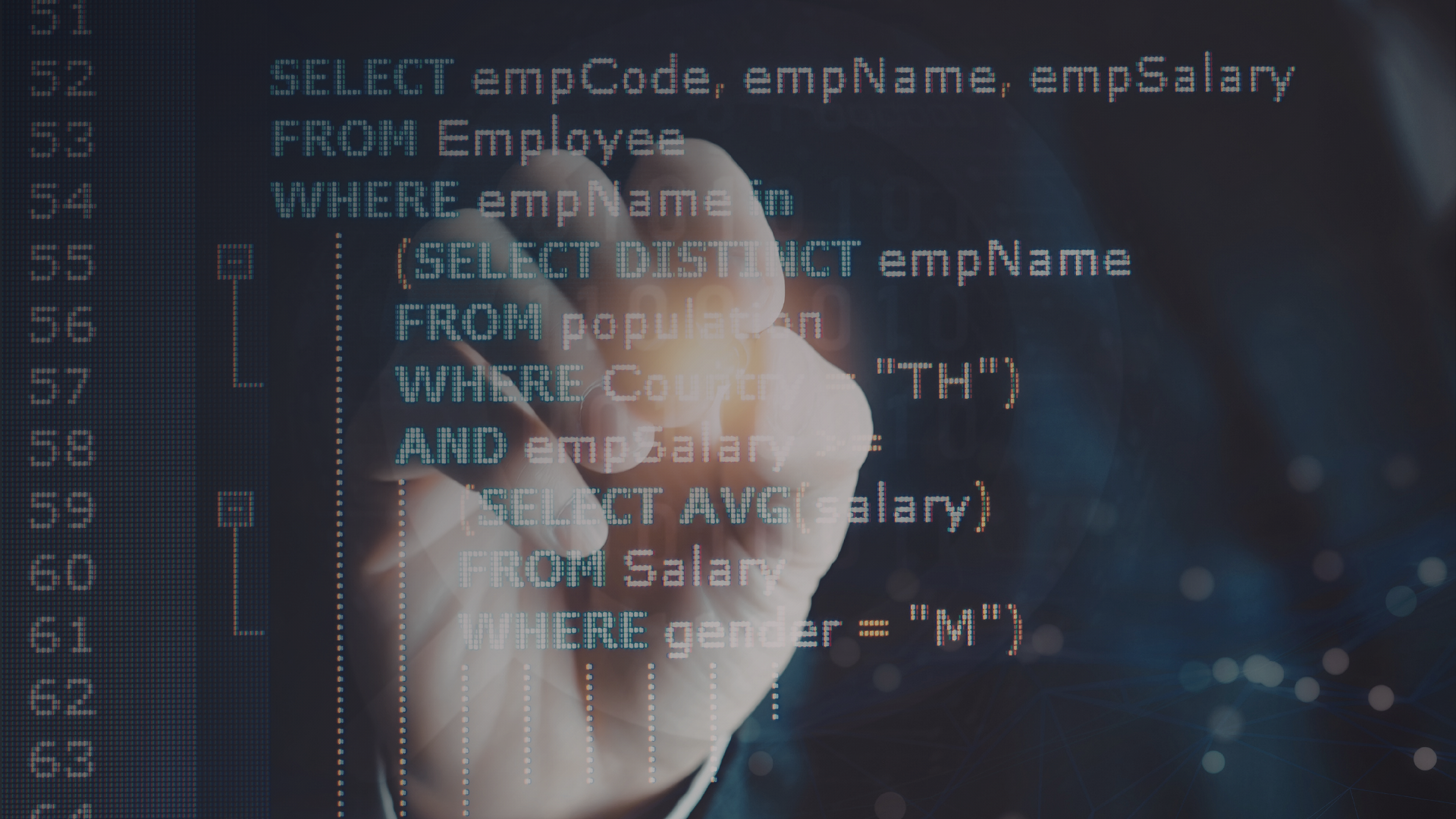
Vibe coding makes it easy to connect a database and start querying data.
You take user input, build a query, and it works.
Until someone sends input you did not expect.
Suddenly your database returns the wrong data. Or worse, exposes everything.
This is SQL injection.
It is not a rare edge case. It is one of the most common and preventable security issues in software.
1. What SQL injection actually is
SQL injection happens when user input is treated as part of a database query instead of data.
Example pattern:
- User provides input
- Input is directly inserted into a query string
- The database executes the full query
If the input contains SQL syntax, it changes what the query does.
Instead of:
- Fetching a single record
It might:
- Return all records
- Modify or delete data
- Bypass authentication
The database is not compromised. It is following instructions.
🟢 Pre-prototype habit:
Never build SQL queries by concatenating user input into strings.
2. Why vibe-coded apps are vulnerable
AI-generated code often:
- Uses string interpolation for queries
- Skips input validation
- Focuses on functionality over security
This creates patterns like:
- “SELECT * FROM users WHERE email = ‘{input}’”
It works with normal input.
It fails with malicious input.
Because security was never part of the design.
🟢 Pre-prototype habit:
Assume all user input is untrusted. Treat it as data, not executable logic.
3. Parameterized queries
The correct solution is simple and well established.
Use parameterized queries.
Instead of embedding input in the query:
- The query structure is fixed
- User input is passed separately as parameters
The database treats parameters strictly as data, not code.
Benefits:
- Prevents SQL injection
- Keeps queries predictable
- Works across most database systems
🟢 Pre-prototype habit:
Use parameterized queries or prepared statements by default. Do not rely on manual escaping.
4. ORMs and abstraction layers
Many developers rely on ORMs to simplify database access.
ORMs can help:
- They often use parameterized queries internally
- They reduce direct string manipulation
But they are not foolproof.
Risks:
- Raw query execution bypasses protections
- Misuse of query builders can reintroduce vulnerabilities
🟢 Pre-prototype habit:
Even when using an ORM, understand how queries are constructed and avoid raw string queries unless absolutely necessary.
5. Input validation and sanitization
Validation is not a replacement for parameterization, but it adds another layer of protection.
Examples:
- Enforcing expected formats
- Limiting input length
- Rejecting unexpected characters
This reduces the attack surface.
But validation alone is not enough.
🟢 Pre-prototype habit:
Validate inputs for correctness, but always rely on parameterized queries for security.
6. SQL injection in modern architectures
Even with modern stacks, SQL injection still appears:
- Serverless functions building queries dynamically
- APIs exposing database filters
- Admin tools with flexible query inputs
Anywhere user input influences a query, risk exists.
🟢 Pre-prototype habit:
Identify every place where user input interacts with a database. Apply the same protection consistently.
7. SQL injection and AI systems
AI applications introduce new risks:
- User prompts influencing database queries
- Generated code creating unsafe queries
- Dynamic query construction based on natural language
Without safeguards:
- AI can unintentionally generate vulnerable queries
- User input can indirectly manipulate database behavior
🟢 Pre-prototype habit:
Never allow AI-generated or user-provided input to directly construct SQL queries without strict parameterization and validation.
8. Hidden edge cases
SQL injection is not always obvious.
Examples:
- Search filters with dynamic fields
- Sorting parameters passed from clients
- Partial query construction in different layers
These often bypass standard protections.
🟢 Pre-prototype habit:
Review any dynamic query logic carefully. Small gaps in protection can create vulnerabilities.
9. Quick pre-prototype checklist
| Checklist Item | Why It Matters |
|---|---|
| Avoid string concatenation in queries | Prevents injection vulnerabilities |
| Use parameterized queries | Ensures input is treated as data |
| Validate user input | Reduces unexpected values |
| Limit raw query usage | Avoids bypassing protections |
| Review dynamic query logic | Identifies hidden risks |
| Treat AI-generated queries carefully | Prevents indirect vulnerabilities |
Closing note
SQL injection is not a complex problem.
It is a simple mistake that has serious consequences.
For vibe coders, it is easy to focus on getting things working and overlook how input is handled.
But this is one area where small decisions matter.
🟢 Pre-prototype habit:
Before writing any database query, decide how user input will be handled safely. If input can reach your query, it must be treated as data and never as code.
See the full list of free resources for vibe coders!
Still have questions or want to talk about your projects or your plans? Set up a free 30 minute consultation with me!